Полная версия
Binary code: Mystery number one
– You mean the NSA is not officially authorized to engage in eavesdropping on US communications systems and does so through cooperation with foreign allies conducting radio intercepts on US soil?
– Yes, that's right.
– I'm directly familiar with it.
– Here, draw conclusions. That's what we're supposed to agree on. And remember, Echelon 2 never fails. In case of detection, you're just a traitor, a spy. Echelon 1 will deal with you, as they should. It's a solid defense, with consequences. If you betray your own, disclose data about its existence, you will be identified, captured, arrested by Echelon 1 under the command of Echelon 2. Understood?
– I'm starting to realize
– All righty then. Take a look at the paperwork. If there's anything you don't understand, just ask. First of all, study this data, which you will work with directly.
He handed over a folder with a red line crossed out.
– That's all for starters. I'll be in my office, the rest of the local details will be provided by the staff directly reporting to you.
Saying the last, the chief raised his index finger upward while making a meaningful expression and left for his room.
Rutra looked around his new workplace, the operations and workroom, met his staff, returned to his office, and went over the contents of the folder. The folder contained one main document and many comments on it. Rutra began to study it. The document contained the following information: "List of computer surveillance and electronic intelligence programs by country. The list contains a list of computer surveillance and electronic intelligence programs implemented or currently being implemented by governments around the world, as well as international projects in this area.
Ruthra knew everything well, but still looked over the important ones:
International
"Echelon" is a global electronic intelligence system operating under the radio and intelligence security agreement of Australia, Canada, New Zealand, the United Kingdom and the United States, also known as UKUSA.
SOUD is a classified information interception system created by the USSR and Warsaw Pact countries to conduct global electronic reconnaissance. It is still in operation today.
National
UK
IMP is an initiative to enhance the UK government's ability to legally intercept communications and store the resulting data in a single database.
Tempora is a covert computer surveillance program launched in the fall of 2011, used by the UK Government Communications Centre in conjunction with the US National Security Agency.
The Impact Nominal Index is a computer system designed for police and other security agencies in the UK that allows them to make quick inquiries about persons of interest.
Russian Federation
SORM – a system of technical means to ensure the functions of operational-search activities. A set of technical means and measures designed to carry out operational-search activities in telephone, mobile and wireless communication and radio networks.
A distinction should be made:
SORM-1 is a system of wiretapping organized in 1996;
SORM-2 is a system for logging Internet accesses developed by a working group of representatives of the Russian State Communications Committee, the Russian Federal Security Service, the Central Research Institute of Communications and Glavvyaznadzor;
SORM-3 is a system for collecting information from all types of communications and its long-term storage.
U.S.
The U.S. Intelligence Community is a system of 16 intelligence agencies whose activities include computerized surveillance and electronic intelligence.
STRATCOM – A special cybersecurity task force in U.S. Strategic Command; integrates nuclear, space, and missile defense.
MAINWAY is an NSA database containing metadata on hundreds of billions of phone calls made through the four largest phone companies in the United States: AT&T, SBC, BellSouth, and Verizon.
Stellar Wind is an electronic communications tracking program, including monitoring email messages, phone calls, financial transactions and internet activity.
Tailored Access Operations (TAO) is a division of the NSA created in 1997 that engages in active and passive surveillance of computers, including hacking and backdoor installation. It is capable of collecting approximately 2 petabytes of network transmitted data per hour.
Boundless Informant is an NSA system for analyzing global electronic communications. It has a huge database, including 14 billion reports on Iran, 6.3 billion on India, and 2.8 billion on the United States.
PRISM is an in-depth Internet traffic surveillance program formally classified as top secret; adopted by the NSA in 2007 as a replacement for the Terrorist Surveillance Program.
DCSNet is an FBI surveillance system that can wiretap any telecommunications device located in the United States.
Main Core is a database that stores personal and financial information on millions of U.S. citizens who may pose a threat to national security. The data is sourced from the NSA, FBI, CIA, and other government sources.
Magic Lantern is a keylogger program sent by the FBI as an email attachment. When activated, it acts as a Trojan horse and allows the FBI to track the activities of an Internet user.
Narus Insight is a cluster-class supercomputer espionage system designed to sniff and analyze network traffic data on the Internet. It uses the Carnivore system as auxiliary data delivery nodes. The operator of the system in the United States is the FBI; users are all U.S. federal agencies.
Carnivore is an automated espionage system for listening to information from websites, analyzing databases on websites, and opening and analyzing emails; an analogue of the Russian SORM-2. An element of the Narus Insight total surveillance supercomputer cluster.
Terrorist Finance Tracking Program – a joint program of the CIA and the U.S. Treasury Department to gain access to the SWIFT transaction database. According to the U.S. government, efforts to counter terrorist activities were compromised after information about the existence of the program was leaked to the media.
X-Keyscore, a secret computer tracking program, is run jointly by the U.S. National Security Agency, the Australian Radio Defense Agency, and the New Zealand Government Communications Security Service. The FBI has created and is actively populating the world's largest database of biometric information on U.S. citizens, including retina, fingerprints, facial structure, scars, voice, language, facial expressions and gestures.
Israel
"Medusa-1" is a program that uses microwave radiation from cell phones to target the subcortical layer of the human brain in order to induce reactions in the brains of those being irradiated that the irradiators want.
"Medusa-2" is a program using DISP Biometric Sensing technology, which uses point detectors of infrared radiation to determine a person's location and posture. With DISP Spectroscopy, the military and gendarmes are able to analyze chemicals in any body tissue, including blood, from a distance.
"Medusa 3" is a spy analysis program.
The users of these programs are:
–Unit 8200 – Responsible for collecting and deciphering electronic intelligence;
–Unit 9900 – Responsible for collecting and deciphering photographic data from aerial and space-based media;
–504th Division – Responsible for gathering information through agent networks and informants;
–Department of Information Security;
–military censorship;
–Operational Management Division ;
–Special Operations Connection ;
–Sayeret Matkal special unit ; Psychological Operations Center;
–Military Intelligence Directorate .
A special place is occupied by Unit 8200, an electronic intelligence unit, part of the Military Intelligence Directorate "AMAN", which collects and decodes electronic information. It is one of the largest such units in the world. In military documents it is listed as Central Collection Unit of the Intelligence Corps. In terms of functions performed, it is comparable to the U.S. National Security Agency.
The Israeli intelligence agency Mossad uses (semi-legally, through fake civilian firms) spying devices that record, through legal and illegal video cameras installed in public places, what is happening in major cities around the world. This is done by Verint, a classified branch of the Israeli intelligence agency Mossad.
This and other Israeli firms have been contracted to tap the phones of citizens of the United States, Canada, European Union countries and Russia, install and maintain, under the guise of office computer programs, spyware components installed in ministries and departments, government agencies, schools, universities, hospitals, etc. All information received is analyzed by the Meduza-3 program.
Rutra looked through the data on other states without emphasizing it. He knew everything about his line of work and more.
It was enough for a start. In the evening, Ruthre was brought his new "official" documents, his security clearance cards and passes, from which he learned that he was now a researcher at a secret institute. Then he was led outside by a security officer through a chain of corridors, elevators, and labyrinths, through the "official" entrance, which was the entrance hall of the closed research institute.
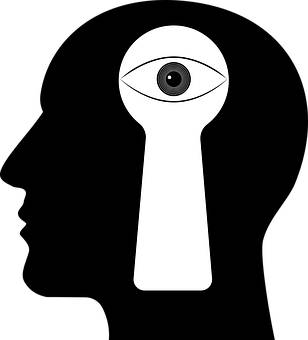
Chapter 3. I can see you, but you can't see me
The next day, Rutra was personally greeted by Vasilyevich. He had a joyful face. Literally from the doorstep he began to teach Rutra.
– What's the first rule?
– Up to 80% of information can be obtained from open sources, the main thing is to be able to understand it correctly," Rutra answered boldly.
– The second one?
– If you want to hide something, put it in the most visible place.
– Third? – The examiner kept up.
– Don't get caught," Ruthra summarized, studying Vasilievich's reaction with a slanted gaze.
– You make me suspicious, though I think we understand each other. We'll work together," the colonel summarized and continued: – For example, such a situation: let's say we send our satellite to the satellite providing communication of the international information service. What do we want to know? Missile launch codes? Troop movements? The background radiation of the strategic command center? No! We want to know how they keep this whole system running. That's what we did during the Cold War when we had the doctrine of total annihilation. And when we realized we couldn't do that without damaging ourselves, we came up with the doctrine of weakening and subjugation. You know what I mean?
– I'm starting to realize
– Something like that. So now the main efforts of intelligence are aimed at finding out who, when, where and how much currency has been made. If we are a rich state, it means that we live well and can influence the world around us. We are a force to be reckoned with, we can develop new weapons. And if we are poor, no one needs our goods, we can temporarily resist with weapons, use internal propaganda, but we will still slip into poverty, dictatorship and, as a consequence, into the social abyss. However, as they say, the truth is somewhere near. The fact is that all important scientific information from all advanced institutes of the world, patent offices, research centers, certification and logging centers flows to the center. Therefore, "big brother" always knows in advance – what, who can do, can influence it. And yet it is no less important to know the banal statistics. For example, if somewhere in a third-world country there is exploration for minerals, which, due to its technological backwardness, this country can neither extract nor use, then we are interested in this, as it is not only us. The world has long been divided, everything is interconnected. Or some state will dramatically increase its consumption of rare earth metals. We calculate what it is for and what it does, in what product it is possible to use it. Therefore, all the goals have already been defined, niches are occupied. If there is a change in some market, what does it mean? That someone needs something more. Some state suddenly orders some kind of equipment for mines, for example. For what purpose? To mine something. What can it extract? All this is analyzed, the relationship is studied. What can be produced from this raw material? How much machinery is purchased? When? Service life? Capacity? This makes up the chain.
Ruthra glanced obliquely at Vasilievich. They were almost at the entrance to the central hall of Zero. Vasilievich continued nonchalantly:
– That's roughly what you were doing, except you were analyzing when, for example, the lights went on in the encryptor's office and when they went off, how to make a multi-stage chain to figure out the encryptor, to get into his social circle, to somehow launch an artificial mouse close to his post, which, after sneaking closer, would scan the contents of his machine by communicating with his smartphone through his computer mouse. That's assuming you still have to get in there, or it can be done from a satellite. From that, you concluded what and how he encrypts, when and what telegram he's working on, what's in it, who it's from, who it's addressed to. And another custodian analyzed another office of the same kind, where it came from, from which dignitary. Your next colleague analyzed who came to this person, his circle of communication, where the command came from, how it was processed, where it went, what happened afterwards. From all of this, a picture was formed of what command was communicated, what was the meaning of it, what consequences it led to and why. And if it was possible to intercept the encryption, we knew that its content was this consequence. It's roughly the same here, but it has to do with the end result of it all, with power and money. With a lot of power and a lot of money. The president of an oil-bearing country sneezed – the price of fuel went up somewhere. The president of a multinational company took a test – we should know the result… Soon civilian technology will surpass military technology. We should follow the development of laboratories by calculating the contracts for the receipt of goods and raw materials. Why? Because no one has ever abolished lying. So we can't be deceived. Control, control and control. Stocks, bonds… You'll do that too. Analyze the same thing, but from the other side. It's an important indicator of the consequences of a planned or planned event. I'm interested in everything: statistical summaries, statistical data. A lot of data will flow to you.
Rutra listened attentively and absorbed everything like a sponge, and Vasilievich kept talking:
– Now our spies are working on civilian projects. For example, new materials, technologies, computer programs are being developed in some state. We want to know how many enterprises, firms are opening, how many are closing, how many of them are engaged in wholesale, how many and what they produce, where they take it, what is their ability to reduce prices, how much the product costs them, when construction will be completed, the unemployment rate. How the science and technology sector is doing. What are the promising developments. These are the ones that are primarily used in the military sphere. Yields, climate, social sphere, their interconnection, prospects for change, first persons, and not only in politics, their contacts, family and business ties, religious, social, political preferences. Everything should interest you. Analyze everything and anything, and put it into a predictive matrix, so that you know not only what they want to do, not only what they can do, but what they will think, even if they don't think they will think it. All the information is very necessary. It makes up the picture of a country's economy, and the picture of a country's economy is its pulse. The way it beats determines how this state lives. Anyway, get started. You will have several assistants, they will analyze the information, collect and systematize. How the program works on the computer will be explained to you. It shows events in real time, and you will know what is happening on planet Earth. You will get any information, including secret information, concerning politics, military sphere, economy. Where what is being developed, where what is being extracted, in what condition the fixed assets are, what ships, trains, airplanes, automobiles are going where, when they will reach, what they are carrying. You have to calculate possible variants of changes in market conditions, new technologies, fulfillment and non-fulfillment of contractual obligations. In general, all sorts of things. You'll figure it out. Your level should correspond to your rank, but you should know that there are no ranks here, we have to join the civilian life. You will participate in many civic events, forums, exhibitions, seminars, meetings, but nowhere should anyone suspect who you really are.
Ruthra was immediately reminded of a James Bond movie. It was hard to suspect a special agent in him – a drunkard, a smoker, a boozer.
– The assistants will tell you the details, they know you in advance. There's a file on each of them in the safe. Here's the key, carry it with you at all times. Even though it's connected to the entry-exit system, you'll still be asked. And now I have a question: although our system works very well and knows what urine test you will have after the New Year, I would like to know from your mouth how you feel about Jews?
That question surprised Ruthra. It surprised him because it sounded like it was here. He made many inferences from any question and tried to choose the answer that was appropriate in this case. Ruthra answered calmly:
– I'm fine with it. But why the Jews? Are you Jewish?
– No way. You have a very serious and responsible assignment. I don't think you have your own game, the viability of the state depends on it, that is, what can be done with the system.
Having said that, Vasilyevich left. Rutra's brain was working hard. He could not understand the sacred meaning of what he had said last. What did this have to do with the secret center? How could one play his game here? Just as Ruthra sat down at his desk and tried to make sense of his office, there was a knock at the door. It was opened by a girl, tall, thin, with black hair. Rutra noticed that there were other girls behind her.
– Hello! – they said.
– Hello," Ruthra replied.
– We came to find out our mode of operation," said the first one and smiled strangely.
Ruthra replied in surprise:
– What, you get to choose? This is a restricted facility, there are regulations and shifts. Excuse me, who are you?
– Your assistants.
– Then let's get acquainted," Ruthra suggested.
– My name is Katya.
– It's a pleasure.
The girl hiding behind her said she was Yulia, the next one called herself Olesya. They smiled.
– What's so funny? – Ruthra asked.
– There's nothing funny," Katya said. – Can I come in?
– Come on in.
She came close and asked almost in a whisper:
– Did he ask you about the Jews?
Ruthra looked at her in surprise.
– Do you know what his last name is?
– No, I don't know.
– Did he scold or praise the Jews? – she asked.
– I don't know, I don't care. He just asked.
– I hope I didn't offend you.
Rutra looked at the girls and thought, "What are busty young women doing here? What kind of professionals are they?"
– No," Ruthra replied. – Let's talk about work. Tell me all about the center. I haven't been very involved. What did you do before my appointment?
– Analyzing the situation," Yulia said. – We work in Europe and the United States. You also have our senior manager Kristina, financial analyst Natalia and the administrator of the center, who is not in the staff at the moment. Or rather, this position is vacant. There are also specialists of the hall, but they are subordinate to us, according to the direction of activity. They are in another hall, there are 20 of them. The rest of the departments, of course, and their heads are directly subordinate to Yury Vasilyevich.
– What do they do?
– They are engaged in primary processing and analysis of information coming through the lines of the Ministry of Foreign Affairs, GRU, SVR. They analyze everything. Not only how, for example, the serial production of memristors will affect the computing power of data centers, but also, for example, how soon the chicks will hatch in a factory in Denmark.
– What, is that a big deal, too?
– Of course. Every situation counts. You have to do all sorts of gibberish. How will the creation of the ionistor affect the consumption of energy resources and, consequently, their procurement, extraction, production, processing, delivery? How many banks with minus balances, what is changing in bankruptcy law in Liberia, for example, how many cattle will calve, how much grain will be harvested, how tobacco is growing there, the lifespan of satellites, the prospect of using unstable elements, the consumer focus group in fifty years, and so on. Who is registered offshore, which ones, why there and not others? Transfers of finances around the world, analyzing the work of stock exchanges, the reasons why quotes change depending on the time of day and weather. Everything matters.
– I understand," Rutra interrupted. – What does Yuri Vasilyevich do?
– He is exercising temporary control. He's here temporarily and is very nostalgic for his past activities. He doesn't know much about economics. He is a fighter of the invisible front, he came to us from the SVR," explained the woman who appeared in the doorway of the office. – Hello. May I come in?
– You can.
– My name is Natalia and I am a financial data processor.
– It's a pleasure," Ruthra replied.
She smiled and said:
– We're used to everything here, especially after Yuri Vasilyevich.
– To what, exactly? – Ruthra asked.
– To the fact that real first and last names, even our own, we have almost forgotten. But one still wonders why people take those particular ones.
– I didn't just ask about Jews," Katya said and added: – Do you know what his last name is?
Ruthra looked at her questioningly.
– Zhidkov," she said.
Yuri Vasilyevich's voice was heard outside the office door.
– Not at all," he said.
The girls looked at each other and quickly left. Discipline had taken its toll. Yuri Vasilyevich's age, rank, and record spoke for themselves. Zhidkov came into Rutra's office, as if he had been standing somewhere close by.
– I went abroad under the surname of Zhemchuzhin, and when I came here, my documents were still old, so they make fun of me. I worked in Palestine and Israel for a long time, so that's why I've been there. No one trusts anyone there. And how can you trust when you're going to die every day? Everyone hides behind a Janus mask to survive. In order for you to understand what happens in such a serious organization, now we will go by departments and you will get acquainted with everyone and everything.
So began Rutra's first day of work at the new place. Basically, except for the fact that Center Zero was the coordinating center between the secret services and the intelligence agencies, he knew everything else. This was not news to him, as he was aware of the capabilities of the intelligence services.
In the modern world, cynical rationality and the most absurd chaos are intertwined in the most bizarre way. The special services of the world's strongest states can easily track all the actions and movements of a law-abiding citizen, but are unable to prevent major terrorist acts. The Large Hadron Collider has brought science closer to understanding the origin of the Universe, but at the same time domestic obscurantism has reached a level that would have been marveled at even in the Middle Ages.
All this creates the most hothouse conditions for the growth of all sorts of conspiracy theories that explain everything that happens in the world as the result of deliberate actions of malicious forces or simply insidious plans of secret groups – from sects and special services to Freemasons and demons. Conspiracy theories have not ignored high technology. You bet, because it is such a tempting way to find simple explanations for the most ambiguous and new events and phenomena!