Полная версия
Digital transformation for chiefs and owners. Volume 3. Cybersecurity

Digital transformation for chiefs and owners. Volume 3. Cybersecurity
Dzhimsher Chelidze
Cover designer Alexander Peremyshlin
Illustrator Alexander Peremyshlin
Editor Alexander Peremyshlin
© Dzhimsher Chelidze, 2024
© Alexander Peremyshlin, cover design, 2024
© Alexander Peremyshlin, illustrations, 2024
ISBN 978-5-0064-4211-5 (т. 3)
ISBN 978-5-0064-2489-0
Created with Ridero smart publishing system
Foreword
Hello, dear reader. This is the final book on digitalization and digital transformation. In the first book, we looked at what digitalization and digital transformation are, why they are needed, what is the difference, what are the pitfalls. In the second they were introduced to the system approach, which is applicable not only for digital transformation, but also in general for any business. The system approach combines proven tools and digitalization, is accessible to anyone and aims to increase the impact of digital technologies, as well as to minimize the risks associated with the organization of work. At the same time, in the first part we talked that in the role model for digital transformation a specialist in information security is needed. Additionally, this is the direction I decided to devote a separate book.
It would seem that digitalization and cyber-free are incompatible, but it is impossible to continue digitalizing without befriending them. Recently at Denis Batrankov I have met a good definition of why it is necessary to deal with information security now: Previously, security was built on the story of the shark: you do not need to be ahead of everyone floating from it – enough to be ahead of the latter. However, now, when you are the target of the shark – it is more difficult to defend”. Additionally, this definition very accurately describes the current situation, as every year hackers’ attacks become more targeted. Additionally, 2022 in general became a landmark.
This book would not have been without the research of Positive Technology (hereinafter – PT), which became my first guides to the world of cybersecurity. Additionally, if you like to immerse yourself thoroughly in the primary sources, details, I recommend you study these studies. QR codes and links to them will be at the end of the book.
The book consists of three parts. The first is devoted to the review and analysis of the current situation. There will be many numbers, statistics, analysts, money. The task of the first part – to form your awareness of the problem and the understanding that information security (hereinafter – IS) – is a direction as strategic as all digitalization, and it is worthy of your attention. The main thesis is at once – a bottleneck in security, as in all digitalization – processes and people, not only yours, but also in the team of software developers (further – software).
The second part deals with the integration of information security from a systems perspective.

Well, the third part is devoted to practical recommendations on what to do here and now, how to choose IT solutions for information security, what people need to know and what competencies are needed.
If you’ve read previous books, you already know my approach – to control someone and delegate tasks, to trust your team, you need at least a basic understanding of its work. And the key task of the whole book is to give you the basic knowledge to build effective work with your team and the IS Director (hereinafter – CISO) with the least labor and risk for you.
Additionally, to avoid any misunderstanding, let’s look at the difference between information security and cybersecurity?
Information security is an activity that involves the prevention of unauthorized access, use, disclosure, distortion, modification, research, recording or destruction of information.
Cyber security is all the same, only related to IT systems and computers.
Part 1. Why deal with information and cybersecurity?
Chapter 1. Immersion and About Money
In 2023, it is already obvious that without the use of digital technologies it is impossible to conduct business, live comfortably, and manage the state.
If we talk about public services, public services in the form of online services are developing around the world. Russia is among the world’s leaders. I, for example, I use the state’s digital services to record a child to a doctor, and to view his vaccinations with test results, and to pay fines, taxes, tax returns.
If we talk about the commercial sector, it can no longer without online: payment for goods, booking tickets, receiving services, consultations, the appearance of digital advisers.
In general, digitalization and automation everywhere. Additionally, if you ignore them, you will be simply uncompetitive. Additionally, if you want to understand what is waiting for us in about 5—10 years, I recommend reading the observations of Yevgeny Bazhov about what is happening in China, in his book Made in China. How to conduct online business in Chinese”.
Let us also, for example, touch on the work with personnel. Without cloud technology and hybrid / remote operation, it will be much more difficult for you to attract talented employees and/or you will significantly overpay for them. Yes, the labor market is changing, of course, and now again the employer is starting to dictate its terms to the average worker. However, this is about the average worker. Additionally, if you want to attract talent, removing is a powerful advantage. According to my personal observations the removal/hybrid saves up to 30—40% on the wage fund. Young, flexible, hungry to the success of the company are actively using it. Additionally, one of the tendencies I see in job openings is that people who want to pay less just give you the opportunity to work remotely. Of course, I do not keep detailed statistics on the closing dates of these vacancies, but they close quickly. It seems even faster than companies with higher salaries, but the requirement to be present at the office daily.
It would seem that this is happiness – digitalization. However, where there are opportunities, there are risks. For example, the development of removals in the year 2020 led to an increase in hacking messengers and collective conference systems. Okay, well, if we could just plug in and crash the online meetings, but the hackers have a different tactic – they copy confidential meeting and chat records to go after extortion. Another modern trend is the encryption of internal files for ransom.
It is also necessary to look at the small developers of IT products: they themselves may not be of interest to anyone, but they may be attacked in order to build into their product malware, and through it attack a large company. Additionally, you can realize such a scenario without even attacking the IT infrastructure – you just need to recruit a remote employee who will make the necessary changes to the code. This approach, when large companies are attacked through contractors and suppliers, is called “supply chain attack”. This is another of the main trends since 2021. In 2022, up to 30% of targeted attacks were on this tactic.
The risks are added by the increase in the complexity of IT solutions, and the decrease in the qualification of the average developer, because the cheaper the developer, the more profitable everything from the point of view of economics. Competition and the market want complex solutions at a minimum price, which obliges to look for ways to reduce the cost of the product. However, all of this leads to an increase in the number of holes in IT solutions. Additionally, you’re not only facing direct financial and legal risks associated with penalties from suppliers and government and criminal liability, but also reputational damage. And if you go public, it’s also the downside risks of capitalization.
The most striking example of this is the attack on SolarWinds. Their clients were US government agencies and over 400 major American companies. Hackers embedded the virus in their solution and attacked their clients. The result is a 40% drop in the value of the shares in a few weeks.
If you look at the absolute numbers, from the beginning of 2017 to the end of 2022, the number of recorded attacks increased from 985 to 2921, that is, an increase of 196.5%. Here, of course, it is necessary to take into account the fact that we have learned better to detect attacks, but, looking ahead, I will say that even now 70% of the companies studied revealed viruses that were not known. The number of targeted attacks increased from 43% in 2017 to 67% in 2022. And although there were 73% of targeted attacks in 2021, the probability of targeted attacks is high. After all, 2022 is the year of the war in cyberspace, real and large-scale.
Now about money. The average ransom price that companies pay hackers is also rising. If previously limited to $1—2 thousand, now it is 4.35 million. The same applies to the maximum payout. In 2017, it amounted to $1 million, in 2022 – already more than 40 million.
The projections are also pessimistic. Therefore, Cybersecurity Ventures expects that the global cost of information attacks will increase by 15% and by 2025 will reach $10.5 trillion per year worldwide, with 6 trillion in 2021 and 3 trillion in 2015.
I will also give you a graph from PT on how the attacks change, who were attacked more often, and who are now in demand among hackers.
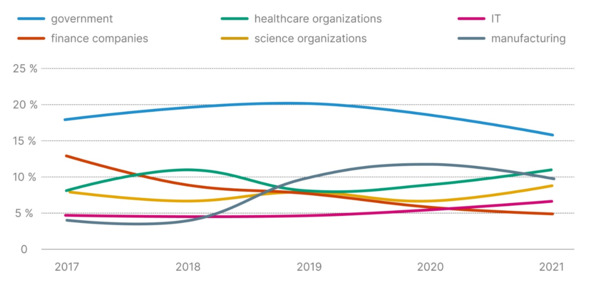
Here I recommend to pay attention to the financial companies – they are less and less interesting as they become more and more complex for attacks. In general, the market of “civil” hacking is more and more subject to the laws of business: intruders are looking for how to reduce the cost of each attack and increase its profitability. Therefore, hackers are looking for margins. However, this applies only to hackers who do not engage in political orders or targeted attacks, for example, from competitors. As a result, given that there is growth away from mass attacks to targeted ones, it is not necessary to rely on one economic expediency of the attack. If you order, you will be attacked. Especially if you are a Russian company. Additionally, if you are the first person, then it is you under the gun in the first place.
Chapter 2. On responsibility
Now the head of the organization is responsible for information security, which is reflected in the decree of the President of the Russian Federation V.V. Putin from 01.05.2022 250. Under its action fall federal executive authorities (federal ministries, services and agencies), management of subjects of the Russian Federation, state funds, state corporations and companies (for example, “Rosatom”, “Gazprom”, “Rushydro”, “RZD” and others) strategic and system-making enterprises, critical infrastructure facilities.
And while on April 20, 2020 the list of system-forming organizations included 646 legal entities, by July 2020 there were already about 1300, and in February 2022 – about 1400. However, you’d think if you weren’t on that list, why would you want it? It is necessary to understand that in our country, if you plan to grow, you will somehow start working with such organizations. This means that it is better to know the requirements of this document and be prepared. Overall, more than 500,000 organizations will fall under the new decree.
What is it recommended that organizations do under this decree?
– Establish personal responsibility for providing IS to the head of the organization, while allocating a separate Deputy General Director, who will have authority and resources to provide IS. It is either necessary to create a structural unit responsible for providing IS or to assign such functions to an existing unit.
– It is necessary to make an inventory of contracts with contractors providing IS services. Now such services can be provided only by companies that have a license to carry out activities on technical protection of confidential information from FSTEC Russia.
– Additionally, on March 30, 2022, restrictions were imposed on the acquisition of foreign equipment and software for subjects of critical information infrastructure (KIA), which make purchases for 223-FZ. Since January 1, 2025, organizations are prohibited from using information protection tools produced in unfriendly states, or organizations under their jurisdiction, directly or indirectly controlled by them or affiliated with them. There are 48 such countries in the spring of 2023. And even if the company supplying IS equipment, for example, from China, you still need to check its affiliates.
Going forward, I’ll make one guess. Taking into account all leaks and the importance of this topic for the state, you can expect the introduction of some insurance, following the example of the CTP. Each organization can be forced to insure against IS-risks. Additionally, then how the organization will build the IS function will influence the size of its premium.
Chapter 3. About General Trends
The main trend in the field of IS – professional managers come to the industry. Those who used to be engaged in “technology”, but now have grown up to managers. They think about the technical side of the issue, as well as about money, the processes in the organization, about the responsibility that they take on themselves. Additionally, this is a serious challenge for IS companies. After all, they need to communicate not just with experts who are in the topic, but find a common language with managers. That is to explain primarily in the language of money and guarantees.
The second trend – the transition from smeared protection throughout the organization, promotion of maturity levels and the use of best practices to a model of guaranteed protection against unacceptable scenarios: disruption of technological cycles, theft of money, confidential information, data encryption. That is, the transition from IS 1.0 to IS 2.0.
This is because everyone is already aware of the impossibility of protection from everything. First, the growth of digitalization and automation has led to an increase in the number of software used. Which means there’s an exponential increase in the number of attacks. Secondly, as we have said before, all IT solution developers try to reduce costs. For example, even the world IT giant IBM transfers its production to India, because there is cheaper labor programmers. At the same time, the quality of the code from most Indian developers leaves much to be desired. It’s like Chinese replicas of original products. All this leads to a decline in software quality and an increase in the number and criticality of vulnerabilities.
Additionally, even published “holes” developers do not hurry to eliminate quickly. Here are indicative statistics from PT. Of all vulnerabilities in industrial IT systems identified and sent to developers in 2021, less than half – 47%. In this case, they become known to the world quite quickly – within a few hours.
In total, about 25,000 new vulnerabilities discovered by security researchers were identified and confirmed in 2022.
The increase in the number of startups and their programs, as well as the failure to comply with the principles of safe development, can lead to this number being only increased.
As a result, it turns out that in more than half of the attacks, hackers quietly use these vulnerabilities and get the necessary access in a few minutes. PT specialists themselves, using known vulnerabilities, were able to access the internal network of companies in 60% of their projects. Additionally, now add the fact that there aren’t many white hackers and researchers, and the developers just don’t know about all the holes. Hackers do not seek to publish found vulnerabilities in the public domain. At the same time, the shadow market of hackers itself is on the rise.
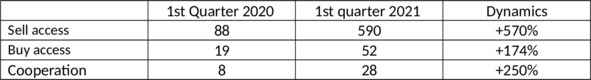
Dynamics of the shadow market
Third, attacks become targeted rather than mass attacks. As mentioned earlier, it was 43 per cent, now it is 70 per cent.
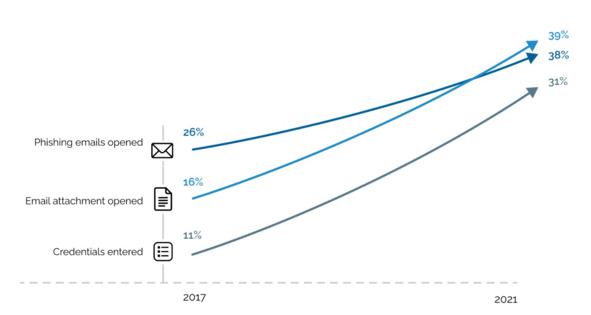
Fourth, no matter how advanced the technology, the bottleneck is still people. Therefore, since 2017, the number of people caught on phishing letters, not only has not decreased, but, on the contrary, has increased multiple. Additionally, in the top most used and effective ways to penetrate the company is still phishing via email. In this case, the topics that people open most often remain unchanged from year to year: salary, bonuses, social programs, DMS, resume. In addition, the best mailing lists dedicated to events in a particular company or division. That is, the growing role of social engineering.
The statistics of attacks against ordinary people are interesting. After all, the endless leaks of personal data make it easier for hackers to choose the right people when planning an attack on the organization. So, in 2021 in 58% of attacks hackers infected users’ devices with malicious software: these were applications for remote control (34%), spyware (32%) and bank trojans (32%). By the end of 2022, spyware was already used in 49% of successful attacks.
At the end of 2022, phishing sites (42% of successful attacks) and emails (20%) were the most common source of infection. Hackers also combined people’s personal devices and organized so-called ddos attacks, that is, simply overloaded the IT infrastructure of the victim organization. Additionally, in massive phishing attacks hackers used the current news agenda: purchase of fake certificates of vaccination, creation of fraudulent sites before the European Football Championship, premiere of a new episode of the series “Friends” or other “delicious” event.
Additionally, fifthly, managers are pragmatic people who want guarantees. As a result, we came to the second trend – the formulation of simple and understandable for top managers queries, so that the unacceptable could not be implemented.
In my opinion, this is quite a normal situation. It is impossible to build up armor indefinitely and close. If you like to drive tanks, remember the example of the Mouse tank, which eventually became sluggish and in life could not move at all, becoming only a museum exhibit. At the same time, the development of technology still made it pierced. In the struggle of armor and projectile always in the end wins the projectile.
Returning to the language of business, I will share an observation. Increasing the armor sometimes leads to the growth of useless bureaucracy. I’ve seen companies close so that business processes stop, and people just go outside the company, start working communication and document exchange in open messengers and personal mail. After all, they have KPI and they require results. And waiting for a week or two until the technical support solves another problem, they cannot. In the end, we want to defend ourselves, but only by multiplying the risks.
The third trend is the development of cyber-polygons and cyber-battles, which provide an opportunity for cyberbes professionals to try their hand at detecting and suppressing malefactors, testing infrastructure and obtaining information for analysis and development. Additionally, since the beginning of 2023, there is active creation of programs to search for vulnerabilities for reward. Such programs are called Bug bounty. This allows “white” hackers and researchers to apply their knowledge for the good and get a reward for it. This applies mainly to the financial sphere (vulnerability search programs) and large corporations (participation in cyber battles).
Chapter 4. What happens in the Industry
Attacks on corporations and organizations are becoming increasingly like planned military operations – attacks on both equipment and people. Therefore, we already know about phishing, exploiting vulnerabilities and so on. However, in addition, there are specialized companies that are developing tools to penetrate various information systems. This is particularly the case in countries where such work is not restricted by legislation. That is, in principle, it is not an illegal business, and given the current situation, many countries are likely to turn a blind eye to it altogether.
Public administration and organizations
State organizations now, in 2022—2023, are undergoing a real combat baptism. In 2022, the number of successful attacks on government agencies increased in every quarter. Government agencies faced the highest number of incidents among any organization. They accounted for 17% of the total number of successful attacks (in 2021 this figure was 15%). In total, in 2022 PT recorded 403 incidents with state organizations, which is 25% more than in 2021.
The main way of attack is social engineering. The target of attacks is data. And this is understandable, because automation and digitalization into the state. Control is well under way. This means that public authorities are beginning to generate big data: taxes, medical information, biometrics, etc. Medical data are of special interest to hackers, including for the purposes of social engineering, increasing the effectiveness of phishing attacks.
The most popular types of malware were cryptographers (56%) and programs for remote control (29%). Additionally, the share of attacks on web resources is constantly growing – in 2020 there were 14%, by the end of 2022 – 41%.
Additionally, government structures are under attack not only in our country.
Example 1
In mid-October 2021, the hacker gained access to the Argentine government’s database, which contains information on all citizens’ identity cards. As a result, on the black-market data and ID-cards of the entire population of Argentina, that is, more than 45 million citizens were put on sale. Moreover, as a confirmation of the data, the hacker disclosed information about 44 known personalities, including the President of the country.
Example 2
Police Department of the US capital Washington. There was a massive leak of internal information after the attack of the extortion program. Thousands of confidential documents were published in the darkwebe (a segment of the Internet that is hidden from ordinary users, where people sell forged documents, weapons, drugs, and hackers orders). Hundreds of police files, informants and intelligence reports from other government agencies, including the FBI and the Secret Service, were also discovered.
Example 3
The hackers’ data encryption attack caused the collapse of the IT infrastructure of three hospitals in the United States, disrupted several routine surgeries, disrupted patient intake, and stole 1.5 TB of personal data, including medical records. The group received a $1.8 million ransom for decrypting the stolen information. A cyber-attack of extortionists on one of the main hospitals of Barcelona (Clinic de Barcelona) resulted in damage to the IT infrastructure of the clinic and forced to cancel 150 urgent operations and up to 3000 patient examinations (according to the Associated Press).
Example 4
Another interesting case was November 2022. At one of the forums in the darkeven there was a report about the hacking of the infrastructure of the Federal Tax Service of Russia. Hackers claimed to have downloaded 800 GB of confidential information. No official comments from the agency were received. The evidence included references to several projects, which according to hackers were taken from the NRF database. “It only took us a week to get into the IRS network, and only three people were involved in the hack. In fact, we have already captured several dozen state structures of this level. However, there is no need to claim them yet,” said the hackers in the message.
At the same time, another curious case with FTS occurred in 2019. Then it was possible to access two databases. The first contained more than 14 million data on people, and the second – 6 million. They included names, addresses, passport numbers, residence data, telephone numbers, TIN numbers, names of employers and information on taxes paid.